Parametri
Maggiori informazioni sul libro
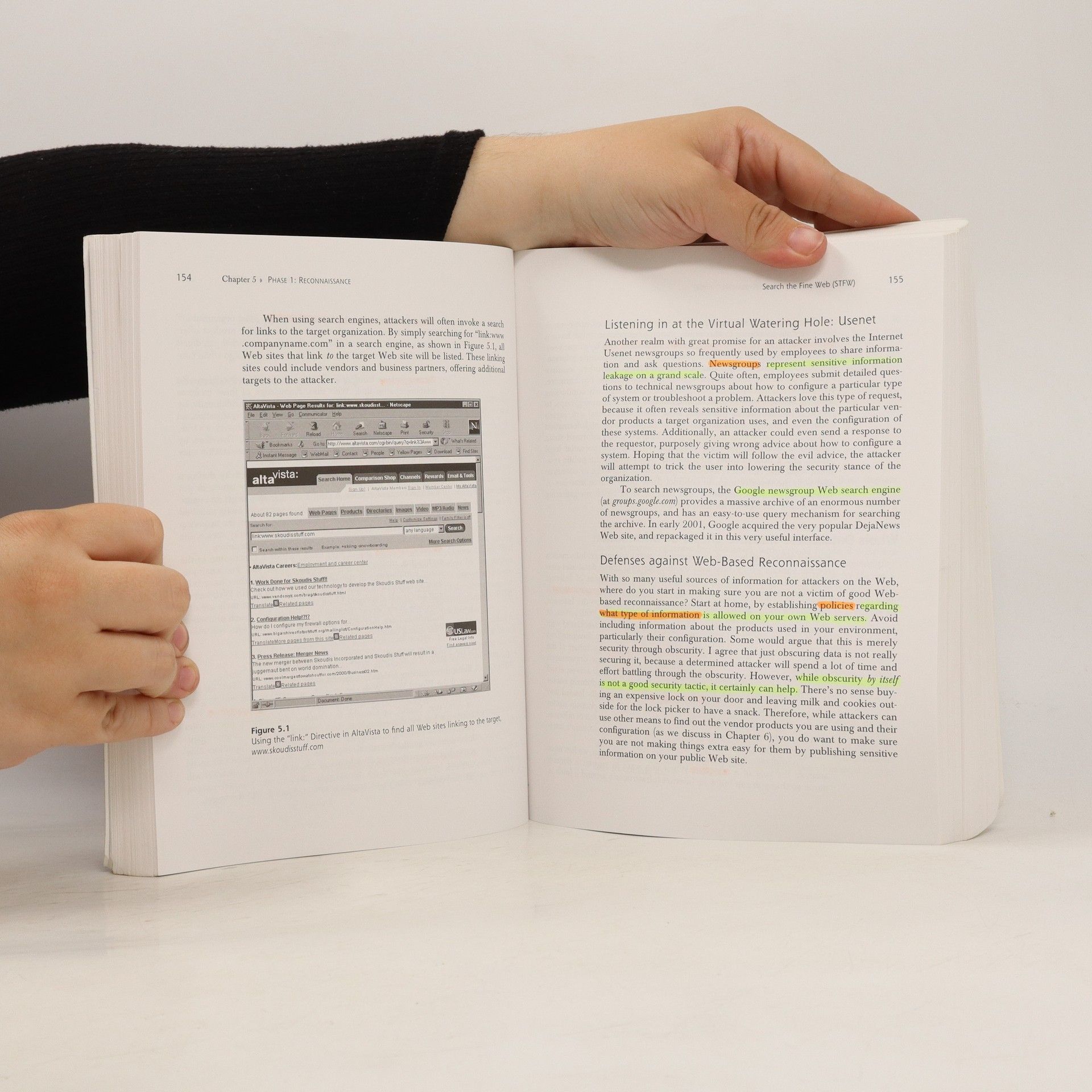
This informal, step-by-step guide will empower every network and system administrator to defend their network assets, whether or not they have security experience. It covers both Unix and Windows platforms, presenting in-depth descriptions of the inner workings of the most destructive hacker tools, and proven, step-by-step countermeasures. Skoudis begins by presenting the hacker's view of networks and their vulnerabilities, with especially detailed coverage of how hackers view the TCP/IP protocol suite. He introduces all five phases of hacking: reconnaissance (targeting of a network); scanning for network vulnerabilities; gaining access and exploiting the system; maintaining access; and preventing detection. Counter Hack presents in-depth descriptions of the most widespread and dangerous attack scenarios, and the most widely-used hacker tools, including war dialers, port scanners, firewall scanners, sniffers, session hijackers, and more. For all system administrators, network administrators, security specialists, and others directly involved in protecting network and computing infrastructure.
Acquisto del libro
Counter Hack, Ed Skoudis
- Iscrizioni / sottolineature
- Lingua
- Pubblicato
- 2002
- product-detail.submit-box.info.binding
- (In brossura)
Metodi di pagamento
Qui potrebbe esserci la tua recensione.